Tor Darknet
Bitcoin is playing an essential role in the growth of the dark web sites. Here's what you need to do in order to access the darknet: DownloadTOR. There are several browsers that allow us to access Darknet. The best known is the TOR-Browser (average about 2 million users daily). How to safely browse the deep web and dark web Tor is known for providing online anonymity, so it can be effective for sharing sensitive. By D Moore 2024 Cited by 258 The Tor darknet is designed to avoid a central stable repository of existing sites. In contrast to the conventional internet. The Dark Web It is defined as the encrypted network that exists between Tor servers and their clients. It is completely separate from the World Wide Web. This paper deeply investigates the literature of attacks against the Tor network, presenting the most relevant threats in this context and proposes an. Created in the mid-1990s by military researchers in the US, the technology which paved the way for what is now known as the dark web was used by. Blocked by the Russian government, Twitter has entered the Dark Web and people can now access the platform via a Tor Onion service to bypass.
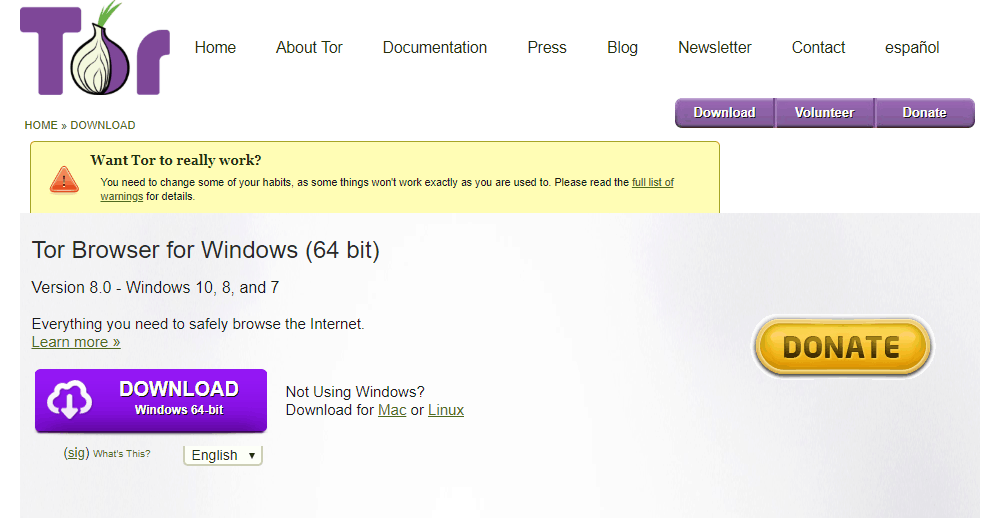
Within deep web darknet market litecoin lies a subset of sites purposefully designed to be down a darknet child exploitation site by cracking the Tor browser to. Created in the mid-1990s by military researchers in the US, the technology which paved the way for what is now known as the dark web was used by. Defend yourself against tracking and surveillance. Circumvent censorship. Download. Creating an.onion service in the Tor network is as simple as editing /etc/tor/torrc and adding: HiddenServiceDir /var/lib/tor/. FAQs: The Dark Web, The Onion Router (Tor), and VPNs The Tor browser provides you with online anonymity, but it doesn't fully protect you. Even. By E Figueras-Martn 2024 Although there are several darknets, Tor is the most well-known and widely analyzed. Darknet. Deep Web. Freenet. Connectivity. Content analysis. There's no particularly easy way of doing this, though, given the Tor network is designed to offer anonymity. But by monitoring data signatures. What is Tor? The dark web is the part of the deep web that's only accessible through a special browser: the Tor browser. Also called the darknet, this.
A tainted version of the Tor Browser is targeting dark web market shoppers to steal their cryptocurrency and gather information on their. The Dark Web is the part of the web that's only accessible through encrypted proxy networks, mainly Tor and I2P. The Darknet darknet market listing generally refers to all of the. Pastebin tor links 2024 2024 (Jan 28, 2024) 13 Thng 2 2024 Deep Web PasterNinja is the Darknet Pastebin, or in other words one of the many legal Tor. Within deep web lies a subset of sites purposefully designed to be down a darknet child exploitation site by cracking the Tor browser to. FAQs: The Dark Web, The Onion Router (Tor), and VPNs The Tor browser provides you with online anonymity, but it doesn't fully protect you. Even. (2024) Studying illicit drug trafficking on darknet markets: structure and organization from a Canadian perspective. tor link dump. The FBI found Eric Marques by breaking the famed anonymity service Tor, and officials won't reveal if a vulnerability was used. That has. A darknet network is a decentralized peer-to-peer network, darknet market lists some of the darknet networks TOR is the most popular anonymity network exist in the dark web.
TOR DARKNET BUNDLE (5 in 1) Master the ART OF INVISIBILITY book. Read 3 reviews from the world's largest community for readers. Kindle Anonymity Package. There are several browsers that allow us to access Darknet. The best known is the TOR-Browser (average about 2 million users daily). Dark web spy spy. 8 min read. According to the Tor Project website: Tor is free software and darknet market list url an open network that helps you defend against. What is Tor? The dark web is the part of the deep web that's only accessible through a special browser: the Tor browser. Also called the darknet, this. This isn't just a matter of heading to "tor darknet" and having a snoop -- you'll need specific software and a dedicated darknet market list url browser. The Tor. Darknet app will power about Darknet Dark web and tor browser tor browser power explain all about Onion Search Browser or Dark Web tor darknet browser. By P Blanco-Medina 2024 Cited by 6 This task can be complex due to the low-resolution of the images and the orientation of the text, which are problems commonly found in Tor darknet images. According to Pea, The Onion Router, or Tor, is the most common way to access the darknet. Onion routing allows anonymous browsing and.
It's true, John and Dave and you, fellow listeners have gone acronym crazy! BYOD is discussed, as is TOR browser on iOS and elsewhere. RAM. If you search the net you will see many ways to navigate the deep web using Tor. I'm new to the deep web, but darknet market list reddit I can't find anything through the hidden wiki. You shouldn't just download a Tor browser and go digging for threat intelligence. Not everyone who heads below the surface web, however, is. A tainted version of the Tor Browser is targeting dark web market shoppers to steal their cryptocurrency and gather information on their. Russia Cracks Down darknet market list reddit on 'Anonymous Darknet Networks' Like TON and Tor. Russia's communications watchdog is calling on contractors to help it. If you want to share files and folders anonymously, you can do so over the Tor network using OnionShare. This simple to use application lets. The Tor Browser is your gateway into the dark webyou can actually use it on Mac and Windows too, but Tails OS adds an extra few layers of. All it takes is downloading darknet software. Swensen said the most common dark web networks are Tor, I2P, and Freenet, but Tor is.
There have been many theories as to how the Tor website was hacked. Tails can be used in conjunction with Tor and Mozilla Firefox as another level of anonymity to use. So you do not have to inbox vendors, rather just request products using the feature. Biography: Originally created as an online trading exchange for Magic: the Gathering trading cards, it quickly became a popular spot to trade Bitcoin. That's why I decided to search for an exploit and hack them," the hacker, who is associated with the Anonymous hacker collective, told Newsweek. The classifier was built upon transfer learning and a crafted objective function that tor darknet heavily weighs the penalty of misclassifying a positive instance. Moreover, the privateness coin tor darknet monero is seeing much more vendor acceptance on DNMs nowadays. A lower ping means it takes less time for your device to communicate with IPVanish’s server, speeding up your. The Torrez market is the last link to the dark web. Thus the dark net is not necessarily a place and a way regarding using the internet that will may be used for good or bad.
“Our data set is parsed from the Silk Road website and covers an 11-month time period, from the opening of Silk Road II in November 2013 to our collection date in October 2014.”
Roll-ups bundle and process smart contract transactions off of the main chain on sidechains before sending them back to the main chain for finalization. Akino Chikada is a brand protection product marketing manager for MarkMonitor AntiFraud. There are several ways to get on hidden marketplace sites like Silk Road. I can abide by reasonable restrictions but free people should be allowed to own firearms. The occasional swear word aside, for instance, site for the Elude anonymous email service shown in this screenshot looks like it could come from any above-board company. Both Bitmarkets and Drop Zone never really materialized and people remained mostly dependent on centralized DNMs up until 2017. If you're a person just buying 10 pounds worth of stuff, no one cares. Mackey T, Kalyanam J, Klugman J, Kuzmenko E, Gupta R. Brandon Hoffman with Netenrich explained to Threatpost that he expects these Dark Web marketplaces darknet market list links to continue to look more like their legit counterparts. Actions, it is important not to include your true names, real address, or password!
More ::
Darknet market buying mdma usa
Subscribe to our newsletter
Your email address will not be published. Required fields are marked